Hello folks,
some time has passed since my last post regarding the GeoIP support for IPFire. In the meantime the funding on the IPFire wishlist hit its goal. Big thanks to all contributors!
For all of you who are desperately waiting for this feature being implemented, there is exciting news:
A test version is available!
Development has finished and first tests have been done. Some minor bugs where found and have been fixed. To get this new feature upstream and shipped with one of the next Core Updates there is still a lot more testing required. Therefore I need the help of the IPFire community.
Getting started
Joining the testing team is a pretty simple task. At first I suggest to everyone to subscribe to the development mailing list to get informed about updated test versions, share experience or simple to get noticed about future developments.
Please follow the next instructions to install the test version:
- Get the latest available test version (001) from here and download tarball to your IPFire test system which has to be at least IPFire 2.17 – Core Update 87 (no ARM test version available) installed.
- Extract the archive by using the following command:
tar -xvf ipfire-geoip-001.tar.gz -C /.
- The GeoIP feature is mainly based on iptables and the responsible kernel module, so the module tree needs to be rebuild with a simple
depmod -a.
- Because of changes in the language files, the cache also needs to be rebuilt by executing
update-lang-cache.
- The final step is to do a reboot of the test system, to take changes in the firewall and automatically get the required GeoIP databases.
As an alternative to prevent a reboot, the firewall can be restarted with /etc/init.d/firewall restart and the databases can be manually downloaded by executing xt_geoip_update.
Usage
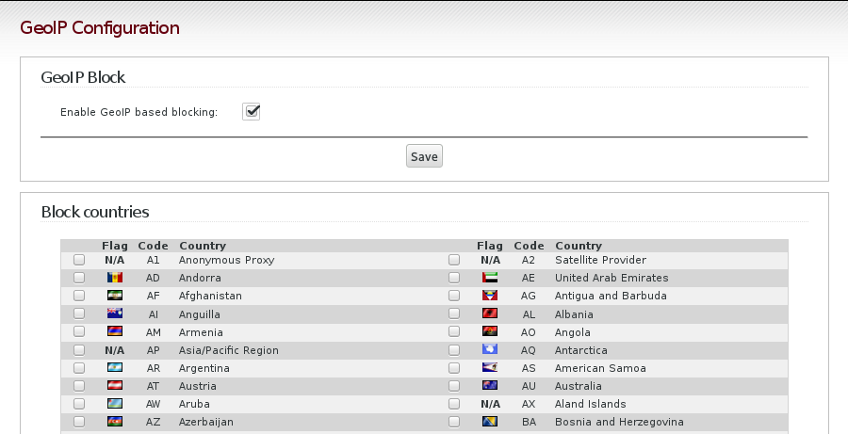
After reboot just get back into the web user interface. You will find a new menu entry in the “Firewall” section called “GeoIP-block” which can be used for a fast and easy blocking of incoming traffic from certain countries.
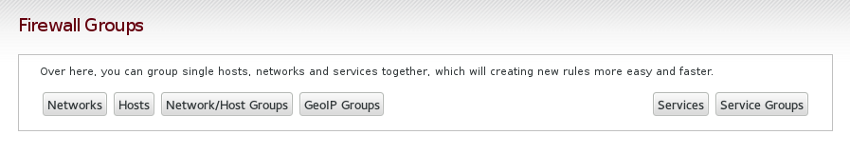
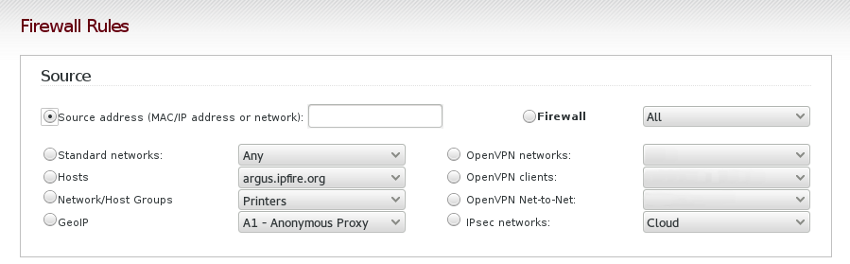
The “Firewall Groups” section has been enhanced to allow creating groups of countries. These groups or even single countries can be used while creating any kind of individual firewall rules on your system.
As usual please send your feedback to our development mailinglist and file any kind of bugs on our bugtracker.